Mail Merge of Microsoft Office
Step 1: Prepare data in Excel for mail merge
The most important step in the mail merge process is to set up and prepare your data. You'll use your Excel spreadsheet as the data source for the recipient list.Here are some tips to prepare your data for a mail merge. Make sure:
-
Column names in your spreadsheet match the field names you
want to insert in your mail merge. For example, to address readers by
their first name in your document, you'll need separate columns for
first and last names.
-
All data to be merged is present in the first sheet of your spreadsheet.
-
Data entries with percentages, currencies, and postal codes
are correctly formatted in the spreadsheet so that Word can properly
read their values.
-
The Excel spreadsheet to be used in the mail merge is stored on your local machine.
-
Changes or additions to your spreadsheet are completed before it's connected to your mail merge document in Word.
Notes: You can import information from your
Excel spreadsheet by importing information from a comma-separated value
(.csv) or a text (.txt) file and use the Text Import Wizard to build a
new spreadsheet.
For more information, see Prepare your Excel data source for mail merge in Word.Step 2: Start the mail merge
-
In Word, choose File > New > Blank document.
-
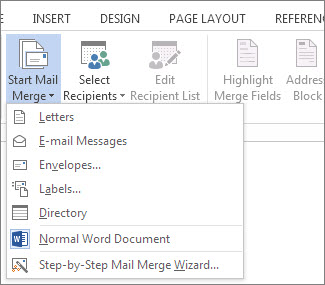
On the Mailings tab, in the Start Mail merge group, choose Start Mail Merge, and then choose the kind of merge you want to run.
-
Choose Select Recipients > Use an Existing List.

-
Browse to your Excel spreadsheet, and then choose Open.
-
If Word prompts you, choose Sheet1$ > OK.Note: Now the Excel spreadsheet is connected to the mail merge document you’re creating in Word.
Edit your mailing list
You can limit who receives your mail.
-
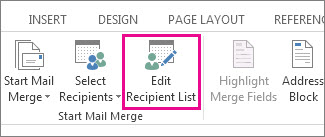
Choose Edit Recipient List.
-
In the Mail Merge Recipients dialog box, clear the check box next to the name of any person who you don't want to receive your mailing.
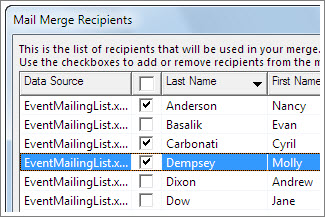
Note: You also can sort or filter the list to make it easier to find names and addresses. For more information about sorting and filtering items, see Sort and filter the data for a mail merge.
Step 3: Insert a merge field
You can insert one or more mail merge fields that pull the information from your spreadsheet into your document.To insert an address block for an envelope, a label, an email message, or a letter
-
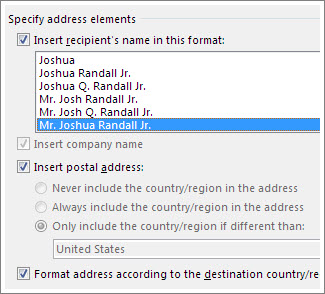
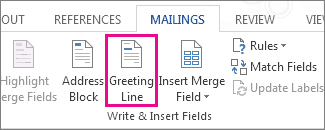
On the Mailings tab, in the Write & Insert Fields group, choose Address Block.

-
In the Insert Address Block dialog box, choose a format for the recipient's name as it will appear on the envelope.
-
Choose OK.
-
Choose File > Save.
-
On the Mailings tab, in the Write & Insert Fields group, choose Greeting Line.
-
In the Insert Greeting Line dialog box, do the following:
-
Under Greeting line format, change the salutation if necessary by choosing the greeting (Dear is the default), the format for the recipient name, and the ending punctuation (a comma is the default).
and
-
Under Greeting line for invalid recipient names, choose an option in the salutation list.
-
Under Greeting line format, change the salutation if necessary by choosing the greeting (Dear is the default), the format for the recipient name, and the ending punctuation (a comma is the default).
-
Choose OK.
-
Choose File > Save.
-
On the Mailings tab, in the Write & Insert Fields group, choose Insert Merge Field.
-
In the Insert Merge Field dialog box, under Fields, choose a field name (column name in your spreadsheet), and then choose Insert.
-
Repeat step 2 as needed, and choose Close when done.
-
Choose File > Save.
Step 4: Preview and finish the mail merge
After you insert the merge fields you want, preview the results to confirm that the content is okay. and then you're ready to complete the merge process.-
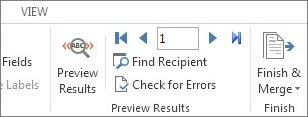
On the Mailings tab, choose Preview Results.
-
Choose the Next
 or Previous
or Previous
 record button to move through records in your data source and view how the records will appear in the document.
record button to move through records in your data source and view how the records will appear in the document. -
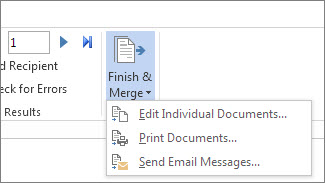
In the Finish group, choose Finish & Merge, and choose Print Documents or Send E-mail Messages.
Step 5: Save your mail merge
When you save the mail merge document, it stays connected to your data source. You can reuse the mail merge document for your next bulk mailing.-
Open the mail merge document and choose Yes when Word prompts you to keep the connection.